
Recordsure partners with Iress to deliver a unique AI solution for financial services businesses
Recordsure partners with Iress to deliver a unique AI

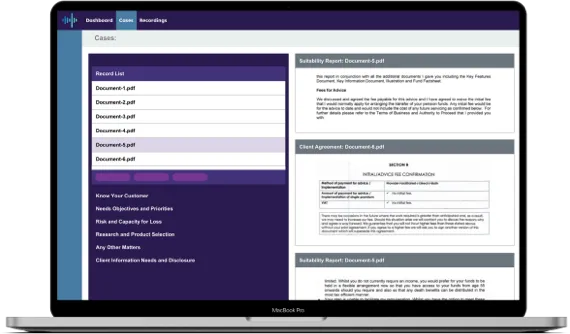
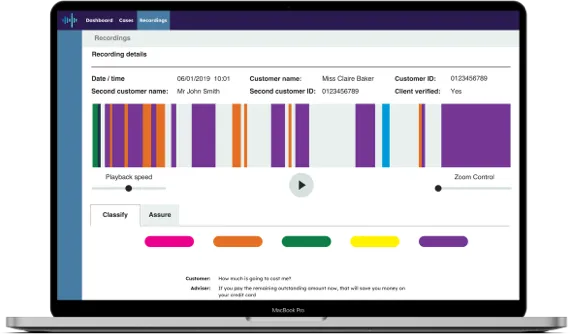
Recordsure Capture app will transform how you record face-to-face and virtual spoken interactions. This tamper-proof game-changing solution allows you to be ‘in the room’ every time, creating an irrefutable audit trail. The app uploads the recordings to our easy-to-search, web-based portal, where you can access them with ease for play back and review.
Fast, smart, consistent and cost-effective solutions for regulated industries.
We understand your business goals and how to achieve them. This is why our solutions enhance your reviews, whatever the scenario.

Our products have a backbone of sector-specific expertise. Years of working with regulated industries
have shaped our approach to delivering more efficient reviews – past and present.
We understand your business goals and how to achieve them. This is why our solutions enhance your reviews, whatever the scenario.
Our proprietary AI is trained on sector-specific conversations and documents, allowing us to target the context and language of your industry. Compared to the simple keyword matching typically used across the AI industry, our sophisticated contextual reasoning methodology yields a higher word accuracy rate.
Our in-house AI training team, linguistics analysts, and speech recognition scientists use in-depth technical expertise to build our AI models. Our specifically trained models apply review frameworks more accurately than humans – every time. And because we do the groundwork, the research, and the technical development, you can start experiencing the benefits of ReviewAI faster.
ReviewAI works hand-in-hand with your specialists, allowing them to focus their expertise more efficiently. Our AI flags up potential risks and pinpoints the exact section that needs reviewing. Thanks to our expertise, your teams can spend their time where it’s really needed.
Backed by the 20 years of compliance experience of our sister company, TCC.
With over 10 years of advanced technology development, research, and industry expertise behind us, you can trust us to understand the things that matter to you.
We put the power of this knowledge in the hands of your teams, so regulated businesses, including major retail banks and government departments, get to experience the benefits of working with us every day.
We understand the importance of keeping costs low without sacrificing the quality of reviews or increasing risks. So, we’re giving you a shortcut to achieving this, powered by ReviewAI.
ReviewAI unique speech and document
analytics tools achieve 100% oversight and
efficient evidencing of outcomes.
ReviewAI unique speech and document
analytics tools achieve 100% oversight and
efficient evidencing of outcomes.
We help our clients deliver more effective and efficient reviews. Here’s how:

Recordsure partners with Iress to deliver a unique AI

The FCA recently released new findings into its review

We’re delighted to announce that we’ve extended our collaboration
We help our clients deliver more effective and efficient reviews. Here’s how:

Recordsure partners with Iress to deliver a unique AI

The FCA recently released new findings into its review
Necessary cookies are absolutely essential for the website to function properly. This category only includes cookies that ensures basic functionalities and security features of the website. These cookies do not store any personal information.
Any cookies that may not be particularly necessary for the website to function and is used specifically to collect user personal data via analytics, ads, other embedded contents are termed as non-necessary cookies. It is mandatory to procure user consent prior to running these cookies on your website.
Uncategorised cookies.
Cookies which provide anonymous data on web traffic which is used to enhance the user experience.
Anonymous cookies collected to enhance the user experience and optimise performance of the website.
Miscellaneous cookies which do not fit in other categories.
Functional cookies which support the user experience.
Anonymised cookies collected to ensure possible advertising content is relevant to users.